As the number and complexity of cyber attacks continue to rise, it is clear that traditional perimeter-based security models are no longer effective. In response, many organisations are adopting a new approach to cyber security: Zero Trust Architecture (ZTA).
ZTA is a comprehensive security model that assumes no user or device should be trusted by default, and that every access request should be fully authenticated, authorised, and encrypted. This article explores the basics and the benefits of ZTA and recommendations for its implementation.
What is Zero Trust Architecture?
Zero Trust Architecture is a security model that requires strict identity verification and access controls for every user and device attempting to access an organisation’s resources – regardless of whether they are located inside or outside of the traditional network perimeter. The ZTA model assumes that all users, devices, and networks are potentially compromised and should not be trusted by default. Instead, access requests must be thoroughly authenticated, authorised, and encrypted before any resources can be accessed.
The core principles of ZTA:
- Verify explicitly: Every access request must be explicitly verified before access is granted.
- Use least privilege access: Access should be granted only to the specific resources required for the user’s role and job function.
- Assume breach: Organisations should assume that a breach has occurred and act accordingly, even if there is no evidence of an actual breach.
- Emphasise security throughout the entire system: Security must be integrated into every component of the system, including hardware, software, and user behaviour.
What are the benefits of Zero Trust Architecture?
There are several benefits to adopting a Zero Trust Architecture approach to cybersecurity:
- Improved security: The ZTA model provides a more robust and comprehensive approach to cybersecurity than traditional perimeter-based models.
- Reduced risk: By assuming that every user and device is potentially compromised, ZTA can help to minimise the risk of data breaches and cyber attacks.
- Increased flexibility: ZTA allows for more flexible and dynamic access controls, making it easier to grant and revoke access as needed.
- Better visibility: ZTA provides greater visibility into access requests, enabling organisations to identify potential security threats more easily.
How to implement Zero Trust Architecture
ZTA is not a one-size-fits-all approach because each organisation has unique requirements and challenges. However, there are some best practices that businesses can follow when implementing ZTA:
- Identify and classify assets: Identify and classify your organisation’s assets, including data, applications, systems, and devices. This will help you determine what needs to be protected and what security controls need to be implemented.
- Implement access controls: Implement access controls that enforce the principle of least privilege, meaning that users are granted access only to the resources they need to perform their jobs.
- Use multi-factor authentication (MFA): Require users to authenticate their identity using MFA to ensure that only authorised users can access resources.
- Monitor and log all activities: Implement a logging and monitoring system that tracks all user activities and network traffic, so you can detect and respond to potential security threats.
- Apply security controls at every layer: Implement security controls at every layer of the infrastructure, including the network, applications, and devices.
- Regularly assess and update security policies: Regularly assess and update your organisation’s security policies, procedures, and controls to stay current with the latest threats and best practices.
- Educate employees: Educate employees on the importance of ZTA and their role in maintaining a secure environment, including training on how to detect and respond to potential security threats.
- Use automation tools: Use automation tools to simplify the process of implementing and maintaining ZTA, such as automated provisioning and deprovisioning of user accounts.
Implementing Zero Trust Architecture requires a comprehensive and strategic approach, involving people, processes, and technology. It is crucial to have buy-in from all stakeholders, including executives, IT teams, and end-users, to ensure a successful implementation. Partnering with experienced security providers can also help organisations navigate the complexities of ZTA and maximise its benefits.
Find out more…
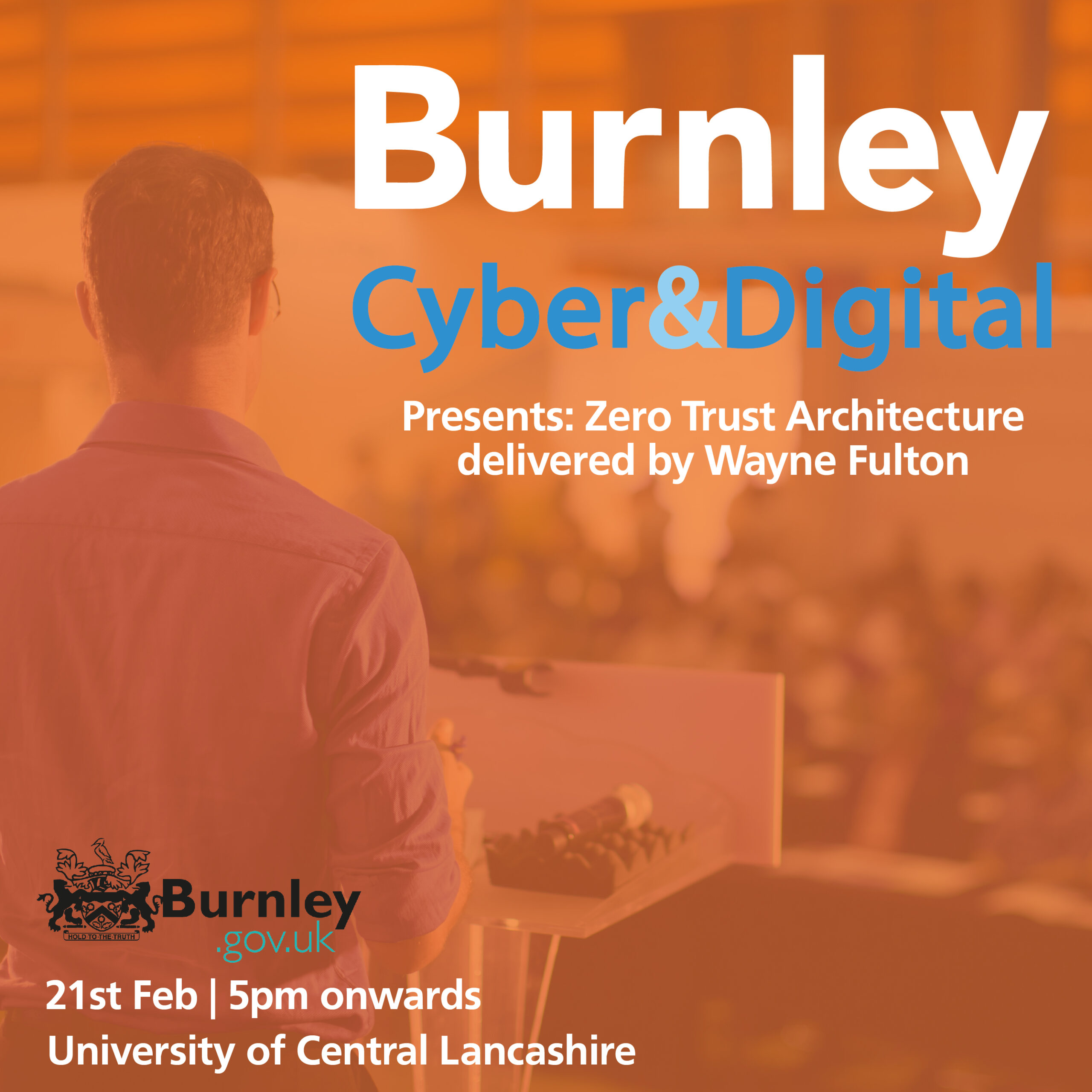
If you’re interested in learning more about Zero Trust Architecture and how it can benefit your organisation, please join us at our upcoming seminar delivered by our Head of Cyber Security, Wayne Fulton. You will also have the opportunity to ask questions at the end of the session.
The seminar is part of Burnley Council’s annual Cyber & Digital event, which will take place on Tuesday, March 21st 2023, from 17:00 to 19:00 at UCLan, Burnley. Attendance is free, but space is limited, so book your place through the Eventbrite link ASAP to secure your spot: https://www.eventbrite.co.uk/e/burnley-cyber-digital-tickets-570521052827
For more information about Seriun and its cyber security services, visit their website: https://www.seriun.co.uk/cyber-security
