Phishing: the red flags
Regrettably, phishing emails have evolved, becoming more sophisticated in terms of format, style, and language. However, there are still clues to identify deceptive emails. If in doubt, it’s safest to delete the email or call the sender using a verified number to verify its authenticity. In most cases, resending the email is the worst outcome. Blocking the sender may not be effective, as such emails are typically sent from disposable accounts with a one-time use.
Follow the tips below to assess your emails to confirm their validity. If they appear suspicious, don’t click any link and delete the e-mail. That’s all you need to do.
No further action is required.
How to detect a phishing attack
Phishing scams are becoming harder to spot as they grow in sophistication and can convincingly mimic a credible source or a reputable company. They always have a call to action encouraging the recipient to download an infected file or click a malicious link. All it takes is one click and suddenly your personal/financial information could be gathered and stolen.
The infographic below looks at the most common red flags in a typical phishing email. Please take time to review them in detail and the explanations that follow.
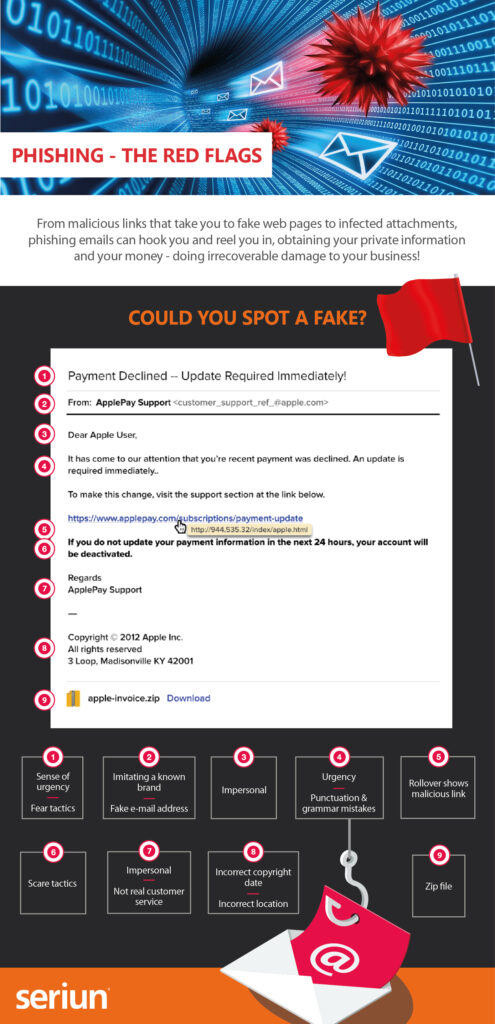
Phishing: the red flags
Subject line
There is often a sense of urgency created in the subject line using scare tactics. A financial theme is quite common for the topic i.e. ‘Your account has been compromised’. The hope is that the recipient will respond without a second thought, and long before they realise it was indeed a scam.
Payment declined – phishing example
‘From’ field
A successful phishing campaign must convince the recipient it was from a credible source. It must have a similar look and feel to that of the company it is mimicking, it must also be written in a similar style – the cybercriminal(s) will have done sufficient research to execute this. On closer inspection you will notice the sender name and email address (as in the example above) are not in the correct format how Apple would normally be presented.
‘To’ field
Be wary if an email comes through which addresses you impersonally with either ‘Dear Customer’ or ‘Dear User’. Even though many legitimate businesses still send out emails en masse when they are promoting an offer or new product, they will still address you by name, especially if requesting an information update for their records.
‘To’ field – phishing example
Body copy
As well as in the subject line, intense language will often be used in the main body of a phishing email. The content will revolve around an urgent plea that attempts to get the recipient to respond without thinking, i.e. ‘Deadline for payment is 5pm’. It is also common for fraudulent emails to be peppered with grammatical errors and punctuation mistakes.
Malicious link(s)
One of the main ways to spot a phishing attack is to scrutinise the link(s). They will usually have been formatted to look convincing i.e. ‘Update your details here’ or formatted to look like it relates to the message and the company the email is purporting to be from (as in the example overleaf). Or the link may have been shortened using an online service like bit.ly. All you need to do is hover over the link with your mouse to reveal the actual address, where you will see it would take you to a different site than stated.
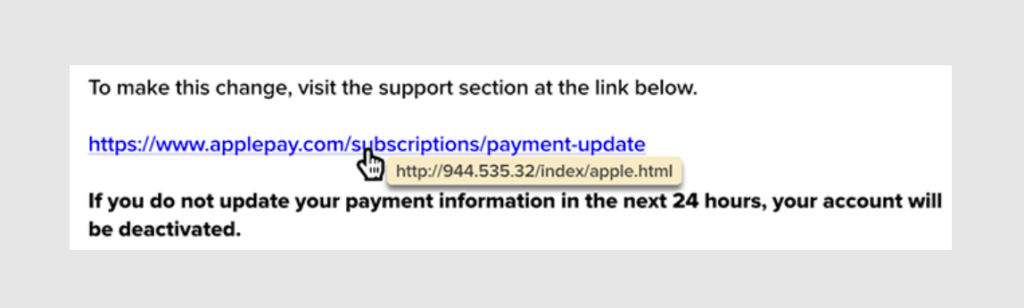
Malicious links – phishing example
Scare tactics
Definitely worth another mention is that scare tactics and intense language are common in phishing emails and can be found throughout the email. The type of content you could expect to see such ploys would be in requesting your immediate response to update your details or make payment within a certain timeframe – usually with a consequence if you don’t (as in the example above). The cybercriminal(s) hope the recipient will click their link(s) out of panic or confusion.
Email sign-off
Similar to the greeting, you will often notice the sign-off is impersonal too – making use of a general title rather than giving the personal touch and disclosing a person’s name and details.
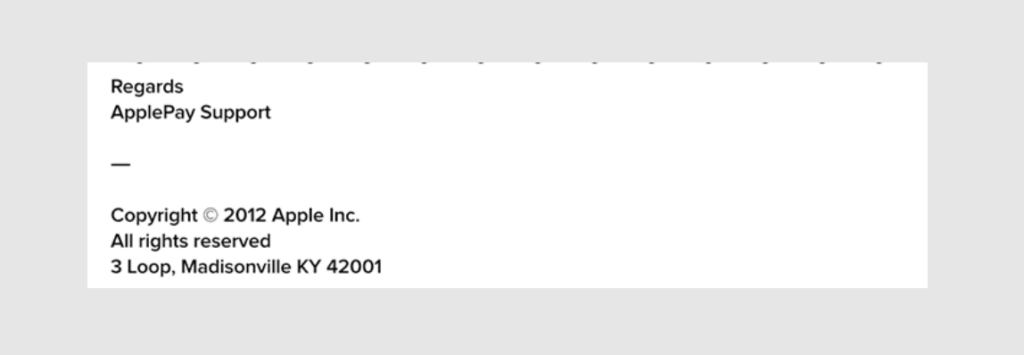
E-mail sign off – phishing example
Footer
Take a close look at the footer in the email. A phishing email may state an incorrect copyright date or a location that doesn’t marry up with the legitimate company details.
Attachment(s)
Phishing emails also can include malicious attachments that contain downloadable or compressed files that may infect your computer. Be wary, if it looks suspicious, it probably is.
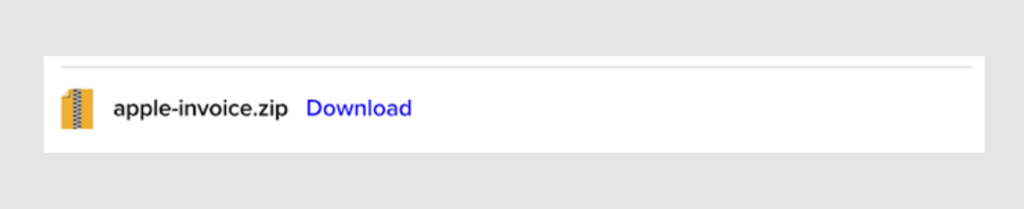
Suspicious attachments – phishing example
Malicious Landing Pages
If you do click on a phishing link, you may be directed to a malicious landing page, like the one below:
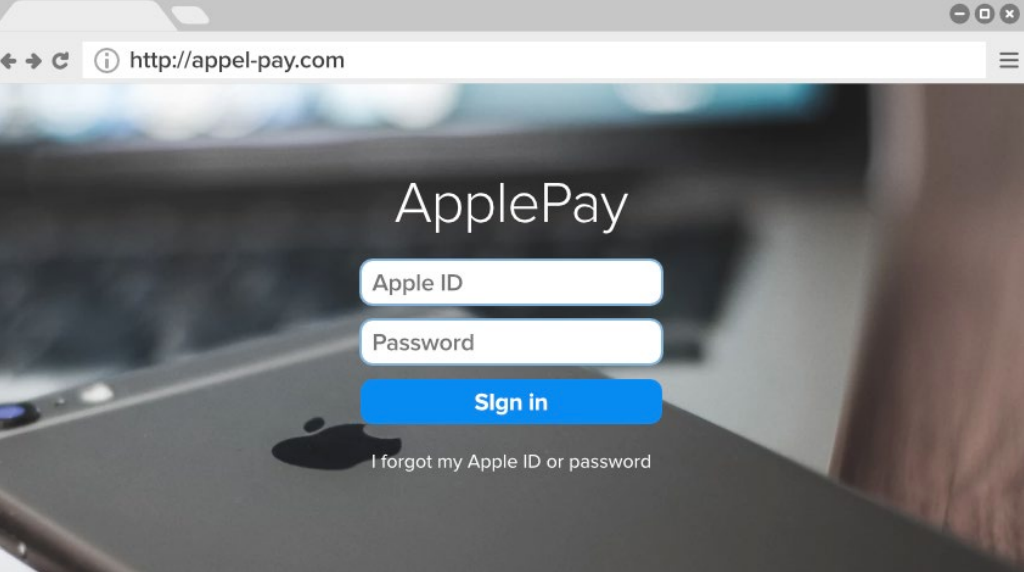
Malicious landing page – phishing example
There are many tell-tale signs that a web page is malicious:
Web address: Despite a malicious landing page doing its best to replicate a legitimate web page, including a very similar URL – there will be some errors there for you to spot i.e. misspellings and unsecure connections. Always make sure there is a padlock icon in the address bar of the page you are in when disclosing personal or financial information.
Missing navigation bar and footer: These pages are often basic, all they are designed to do is to steal your information so are uncomplicated and often won’t include the header and footer. You can see they are missing from the ‘Apple’ sign-in page example above.
Misspelling: Like with a phishing email, you will often find fraudulent landing pages will contain misspelled words, watch out for small oversights like in the above example, where ‘Apple Pay’ is misspelled as one word.
Information collection: The objective of a phishing campaign is to deceive the recipient into freely giving away their personal/financial information. If you click a malicious link you will probably be taken to a landing page like the example above, which will likely have a form to collect your data that differs from the legitimate company equivalent. In the example above, the form requests users to enter their Apple ID password, which is not requested on the actual Apple page.
Talk to our team
We would love a chat about IT Support and Technology!

Burnley Office: Unit 9 Vantage Court, Riverside Way, Barrowford, England, BB9 6BP
_________________________________________
Manchester office: Office 505, Arkwright House, Parsonage Gardens, Manchester, M3 2LF
Burnley: 01282 500770
Manchester: 0161 3883533
Email: sales@seriun.co.uk